Blockchain technology has evolved from a niche technology into a transformative force across industries. Challenges and opportunities increase manifold as the applications of technology expand. The same is the case with this decentralized ledger technology, in which securitization is necessary to combat such risks. In this article, we will explore how blockchain security works, its challenges, and opportunities that arise in a dynamic environment.
Table of Contents
ToggleHow does Blockchain Security Work?
A) Decentralization and Immutability:
Decentralization in blockchain security is a control-transfer process from a single centralized entity (individual, institution, or group) to a decentralized distributed network. This process takes place through a distributed ledger. Each participant maintains a copy of the transaction history. Smart contracts, automate and ensure the execution of predefined rules. In such decentralized networks, achieving unanimity among nodes is essential. Consensus algorithms like Proof of Work (PoW) or Proof of Stake (PoS) achieve code consensus The code for the consensus framework shows how nodes behave for the validity of transactions and the addition of new blocks.
The data entered into the blockchain is immutable which refers to the inability of data to be altered. So, in decentralized blockchains, immutability means the entered data is irreversible. Transactions are permanently recorded and viewable to anyone. It is achieved through the cryptographic hash function. This process works when the blockchain collects transaction information and enters it into a block, like a cell in the spreadsheet consisting of information. Then this information is run through an encryption process which converts it into a hexadecimal number known as hash. Each block contains a hash of the previous block. The block is then entered into the following block header and the encryption process starts again with other information in the block. This process creates a chain. In simple words, it is a series of blocks chained together. Once a block is added, modifying any previous block is infeasible because it has to recalculate the hash for that block and all subsequent blocks.
B) Cryptographic Techniques:
Blockchain is dependent on the principles of cryptography. Blockchains must be secured with cryptography tools to securitize data and transactions. Hash functions generate a fixed-size hash independent of the input data, which means that the fixed-sized hash is unique. This is due to the message digest which can be defined as a one-way hash function. Algorithms are used to create the hash of data like algorithm hashing SHA-256, which ensures its integrity.
Digital signatures are vital in the authorization of transactions. Each party of transaction is provided with both, a public key and a private key. When a party starts a transaction, it is signed with their private key. But other parties have to verify their signature, they do so by using the sender’s public key. The transactions remain original and reliable this way. Cryptographic libraries are used for the generation and verification of digital signatures.
Public-private key pairs maintain confidentiality. Transactions are visible but the parties involved remain anonymous. Users use their public keys to receive funds while their private keys are used for transaction signing. This process comprises generating and managing key pairs and handling encryption and decryption processes. Users can exchange securely this way.
Read More: Top 3 Advanced Web Security Techniques for 2025
Smart contracts, are written in languages like Solidity for Ethereum and implement business logic based on blockchain security. Its code includes prerequisites, procedures, and rules that are executed by default when the pre-defined conditions are met. Smart contracts have to make security stringent, and this is done by a secure coding process, elaborate testing methods, and persistent control methods. Reentrancy, unexpected practices sometimes malicious threats, and integer overflow can fail the smart contracts, we can overcome this failure by reliable coding standards and external audits.
Challenges in Blockchain Security:
A) Attacks and Consensus Mechanisms:
51% of attacks are one of the challenges of blockchain security. These attacks are caused by exposures in consensus mechanisms. In this attack, the entity can take control of more than 50% of the blockchain’s computational power. In Proof of Work (PoW), in which nodes compete to solve complex mathematical problems to add a block, a malicious entity can dominate by more than 50% by renting mining hash power. In programming, reducing this risk involves constant evaluation and enhancement to ensure that the consensus algorithm is in good shape.
For instance, changing the difficulty level of the cryptographic puzzles in Proof of Work can make it difficult for hackers to gain majority control. Proof of Stake (PoS) and other consensus mechanisms that rely on ownership can be used alternatively.
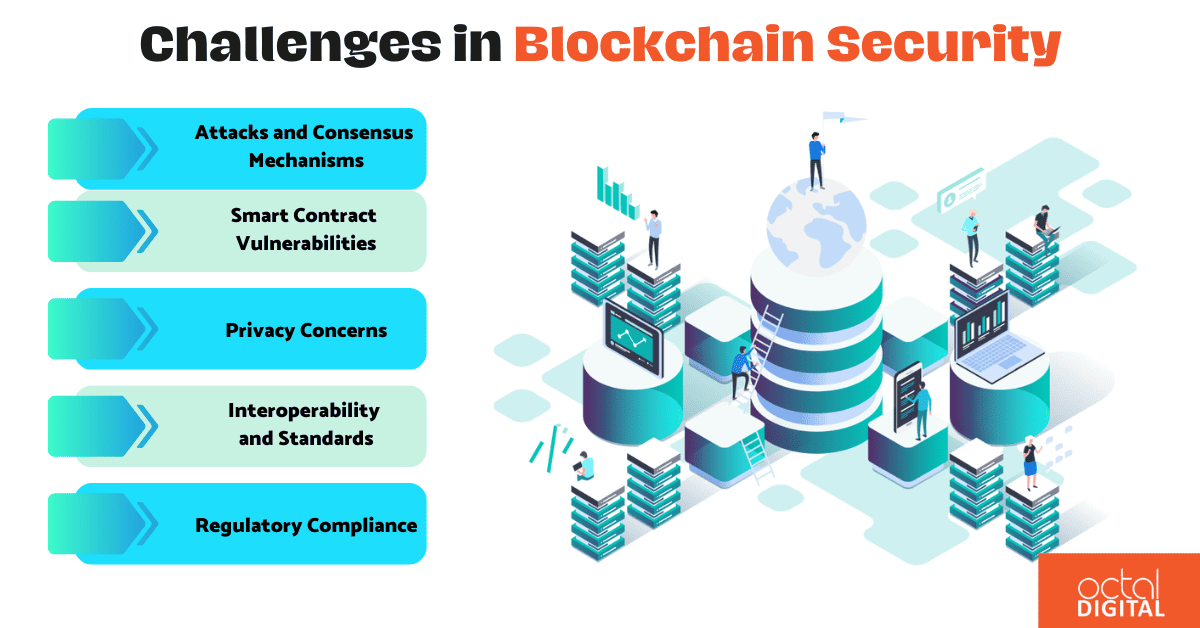
B) Smart Contract Vulnerabilities:
A range of vulnerabilities encompass smart contracts which makes them prone to exploitation. Reentrancy attacks are such attacks where an attacker repeatedly calls a function before the previous calls are completed. This is also one of the challenges. But wait, there is another challenge encountered, and that is Integer overflow where calculations surpass the maximum value a variable can keep. The solution is comprehensive and detailed coding practices and continuous control systems.
While developing the code, secure coding patterns that are resistant to vulnerable constructs must be used. Static analyzers and formal verification tools can scan code to check for vulnerabilities. Adhering to traditional proven techniques, such as input reviewing, utilizing safe libraries, and securing proper access controls must be used by the developers.
C) Privacy Concerns:
The blockchain’s counterfeit nature also provides some degree of anonymity but doesn’t provide much privacy. Developers are needed to integrate privacy-focused techniques into the codebase, especially for data-sensitive industries. For example, zero-knowledge proofs allow you to prove the authenticity of information without disclosing the information.
Implementing consensus mechanisms that focus on privacy, like zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) used in Zcash, needs integrating cryptographic libraries that support these techniques. Confidentiality is sustained during the generation and verification processes in the codebase.
Recommended Read: BloackChain Security in Healthcare
D) Interoperability and Standards:
Interoperability is also one of the challenges. This originates from the not-so-standardized communication standards among numerous blockchain security networks Making these networks secure by protected communication procedures and standardized interfaces is important. This applies to developing application processing interfaces and communication protocols that fulfill the standards.
For example, the Interledger Protocol (ILP) promotes interoperability between different payment networks. Implementation concerns coding communication modules that coordinate with ILP standards. The codebase should be partitioned and flexible to adapt to the changing standards. Any update in the standards and requirements should be incorporated to demonstrate their flexible nature.
E) Regulatory Compliance:
Compliance with the regulations is crucial in the world of blockchain. While developing, private blockchains or compliance-focused tokenization solutions must conform to regulatory frameworks. Put in professional words, this process is done by combining components like privacy controls and tokenization tools with legal requirements.
User privacy is a major concern in blockchain. The codebase should be developed in such a way that it facilitates the traceability and scrutiny of transactions while maintaining user privacy. Such smart contracts that are regulated, keep the decentralized qualities of blockchains while disseminating information to authorities.
We at Octal Digital, a web development company, take your digital journey to skyrocketing success. Our team of highly competent developers can combine state-of-the-art technologies and security measures that are flexible and shaped according to your needs. So, what are you waiting for? It’s time to take your digital journey to high levels of success with Octal Digital. Here we make use of resourceful security while maintaining excellence.
Opportunities in Blockchain Security:
A) Quantum-Resistant Cryptography:
The coding approach to enhancing blockchain security lies in transforming quantum-resistant cryptographic techniques, in the face of the increasing threat of quantum cryptanalysis. RSA and ECC, existing algorithms, are vulnerable to quantum attacks. Alternatives to such assaults include hash-based and lattice-based encryption.
XMSS (eXtended Merkle Signature Scheme) is an example of the integration of libraries in coding to create hash-based cryptographic methods. Lattice-based encryption uses the hardness of lattice issues to provide security. The adoption of lattice-based cryptography uses cryptographic modules. These tools use lattice-based encryption and signature techniques. Blockchain security measures are made more resistant to possible quantum computer invasions by using and implementing those techniques.
B) Immutable Auditing and Transparency:
Blockchain provides special opportunities for open, easily-verifiable record-keeping. This is all due to its immutability nature. Blockchain plays a major role in sectors including logistics and healthcare. It improves the accountability, traceability, and transparency of these sectors because they are info-sensitive. To say the same in technological words, we would say that it generates smart contracts that log and timestamp relevant data. This may include the sources and paths of products in the supply chain or the patient records as in health-related data.
For example, a smart contract for supply chain transparency could record a product’s journey on the blockchain, with zero alteration. Smart contracts allow auditors to verify data integrity. This requires cryptographic hashing and timestamping code signings. Thus, guaranteeing that the immutability of the recorded data is incorporated.
C) Decentralized Identity Management:
Decentralized identity solutions have revolutionized identity management. Now by using blockchain-based identity solutions, consumers are given greater control over their data. The result is that it leads them to a reliance on a decentralized entity. DIDs and verifiable credentials: they are not issued but rather created within the blockchain system itself as a code-enforced practice.
An example would be the use of smart contracts through blockchain security by a decentralized system for identity management. Its main role is to develop and store secure DIDs and credentials, which should be — on the other hand — easily verifiable. The introduction of cryptographic techniques including zero-knowledge proofs guarantees that information about users’ identities will not be exposed unless necessary. This includes data that needs to be kept confidential; it means that the construction of such infrastructure with reliability and security depends greatly on codebase quality.
ovation and security. Elevate your digital landscape with our expert team, dedicated to implementing the best practices and advanced blockchain security services.
D) AI and Machine Learning for Security Analytics:
Blockchain securitization has brought a huge change in the digital arena through advanced analytics that uses AI plus machine learning. There are several tools for example threat intelligence, threat detection, and advanced analytics that use AI. These tools strengthen the security against instant cyber threats. Let’s read that process technologically. It involves creating modules that process the blockchain data and check for any patterns that may indicate malicious activity.
This can be better understood by example, the algorithms of machine learning can understand normal transaction patterns. The algorithm can identify any unusual activity that can show swindling and fraud attempts. Coding in blockchain security analytics demands implementing machine learning algorithms. It also contains analysis of the components, and model training periodically to enhance accuracy.
E) Improved User Education and Adoption:
User education and adoption are very important in the blockchain ecosystem: without them, the technology cannot survive for long. In order to drive user awareness and adoption significantly, the development of user-friendly interfaces along with easy-to-understand instructional materials on blockchain platforms should be implemented. This involves creating interfaces that are easy to use as well as those that promote safe key management— all while users are educated on potential risks plus safety procedures through such instructional materials.
Consider a case study: creating a user-friendly wallet interface puts the spotlight on getting key management right. It educates users on safe transaction practices and guides them on how to back up their details. Platforms inject educational modules as part of their core codebase, reaping benefits from this linkage by obtaining end-user feedback about blockchain security concepts— thus nurturing a clientele that is well-informed and vigilant about security aspects.
In brief, the possibility of creating a security code for blockchain contains quantum cryptography, unchanging auditing, decentralized identity management, AI-powered safety analytics, and user education. Through these measures, blockchain developers can improve security, transparency, and adoption by users. It is assisting in creating a stronger more resistant decartelized future.
Why choose us as your web development partner? Our expert web developers are not just skilled, but they’re committed to securing your digital assets. With a focus on industry-leading security practices, we ensure your website stands strong against cyber threats, providing you with peace of mind and a foundation for sustained success.
Conclusion:
So, the security of the blockchain is not a one-time process but a periodic process. Some challenges that we discussed are the 51% attacks and smart contract exposures. Then, we looked at opportunities arising such as improvements in cryptography and distinctive use cases. Researchers, developers, and industry experts will and are partnering with each other to transform the world of blockchain. By taking farsighted actions in response to challenges and exploiting opportunities coming our way, the time is not far when there will be wide adoption of blockchain with strong security mechanisms.
FAQs:
1. How does cryptography work in blockchain Security?
Cryptography is used in blockchain security. Let us understand this by the example of hashing, it converts data blocks into unique, irreversible fingerprints. But wait, that’s not all; digital signatures verify the source’s authority and transactions. Asymmetric cryptography promotes key handling for smart contracts as well as user wallets. It is done in such a way that ensures a uniform approach to handling various cryptographic functions.
2. What is a consensus mechanism, and how does it impact blockchain security?
The consensus mechanism is the process by which nodes in a blockchain network agree on the validity of transactions and the current state of the ledger. Different mechanisms offer varying levels of security and scalability.
3. What are the security implications of sharding in blockchain security?
Security implications increase manifold when we use sharding. Because it divides the ledger into smaller portions called shards. Transaction speed increases but so does the risk. Sharding creates various attack points for malicious attackers. It becomes a challenge to secure communication and maintain data integrity across different shards.